[!Important]
preg_match过滤绕过及RCE重定向截断
0x01
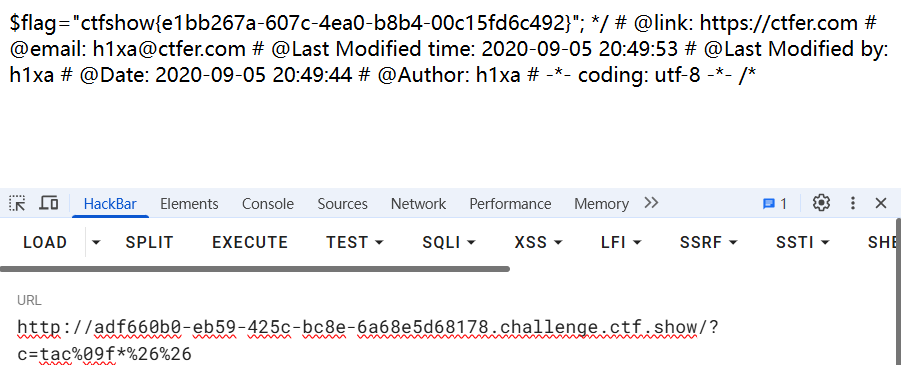
访问靶场,获得源码回显
| |
0x02
[!Note]
代码审计,过滤了
; cat flag 'Space'标准输出被重定向
故此处采用&&替代;,Tab替代Space(常用字符替换)的形式构造payload
0x03
省略目录查看过程,访问flag.php获得flag
[!Important]
preg_match过滤绕过及RCE重定向截断
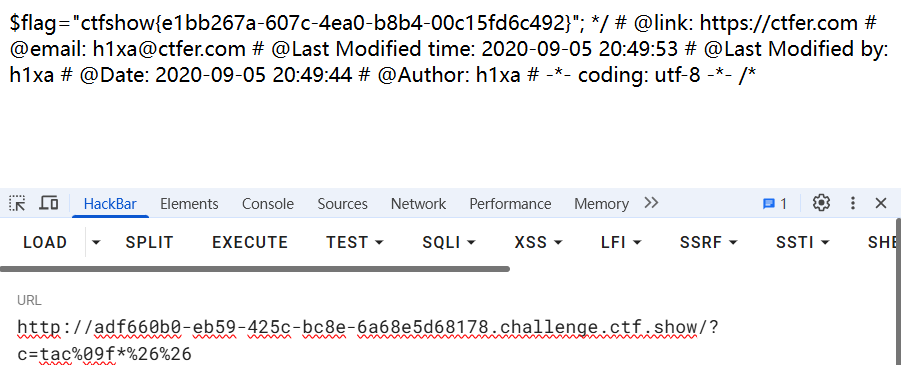
访问靶场,获得源码回显
| |
[!Note]
代码审计,过滤了
; cat flag 'Space'标准输出被重定向
故此处采用&&替代;,Tab替代Space(常用字符替换)的形式构造payload
省略目录查看过程,访问flag.php获得flag